Thunderspy Assault: Vulnerability in Windows, Mac and Linux
Introduction
Well, so after seeing the title above, the big questions arising in your mind now are probably ”what is a thunderspy attack?” and “could my PC be vulnerable to it?”
We will gladly answer those as we get along, but before we do, you need to take a look at certain electronic mechanisms such as thunderbolts, which will help you better understand the whole thunderspying concept.
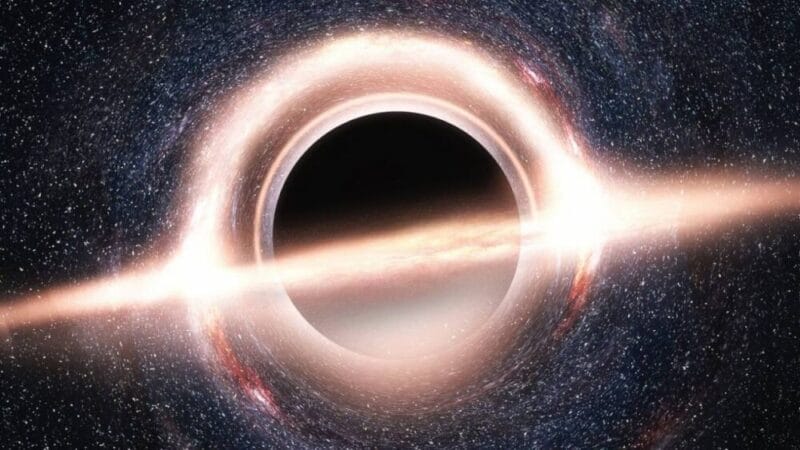
Thunderspy Attack Demonstration
What Are Thunderbolts?
Thunderbolt is an equipment interface created by Intel and Apple to associate peripherals to PCs.
Thunderbolt gadgets have direct access to memory (DDA), which permits them to write input, read the output and keep in touch with the system’s memory while being supervised by the operating system.
One significant expansion of this kind of gadgets is an element called Security Levels, which permits an individual to expressly confide in just a single explicit Thunderbolt gadget.
This gives more straightforward access to the system’s memory, which can prompt security vulnerabilities.
Thunderspy Assault: Vulnerability in Windows, Mac and Linux
How Thunderspy Attacks are Carried Out
Specialists have built up another assault that makes use of loopholes within the defences of the Thunderbolt’s security settings, thereby gaining access to PC information.
Presently, a Dutch specialist has exhibited the capacity to remove this type of physical access from Intel Thunderbolt ports found in a good number of PCs.
This week, it was uncovered that analyst Bjorn van der Meulen of the University of Amsterdam and his group, who called their technique “Thunderspy,” uncovered details of the assault strategy.
The assault, known as a “Thunderspy,” keeps going for about 5 minutes and can be completed without the programmer requiring physical access to the PC being aimed at.
Thunderbolt gadgets, for example, Thunderbolt 2, 3 and 4 might be powerless against Thunderspy assaults.
This is a ground-breaking highlight that aggressors could venture to take information from Thunderbolt peripherals.
The reported Thunderspy assault which influences all PCs made in 2019 and takes under 5 minutes to pull off physical access gadgets, has an effect as indicated by the researchers.
The assault is fruitful regardless of whether the PC is snoozing or bolted and the helplessness can’t be fixed with a product update.

Thunderspy Assault: Vulnerability in Windows, Mac and Linux
A DMA-based assault permits an assailant to destabilise the PC aimed at, by interfacing a DDA (Direct Access Memory) port to the PC’s Thunderbolt port.
This assault exploits a typical Intel Thunderbolt interface in a large number of PCs around the globe.
A loophole in a Thunderbolt part called Thunderclap, revealed by a gathering of specialists a year ago, indicated that a malicious gadget connected to a PC’s Thunderbolt port can rapidly get past its security system.
In a subsequent exhibition, it was demonstrated how an assailant could make use of the Thunderspy vulnerabilities to forever incapacitate Thunderbolt security.
This could be done by influencing a PC user to launch a firmware update and then writing an altered, uncertain duplicate to the SPI streak on the gadget aimed at.
The aggressor at that point associates a Thunderbolt-based, Intel Thunderbolt 2, 3, or 4 gadget with a PCILeech to the PC which he/she is aiming at and utilizes it for the loading of a kernel module that permits the assailant to backdoor the login screen, thereby gaining full PC access.
Ruytenberg’s new method permits an assailant to get past even these security settings by changing the security method of the Thunderbolt port and changing its security settings to permit access to the gadget.
Ruytenberg had the capability to change the firmware of the Thunderbolt control chip to get across this component and empower different gadgets.

Thunderspy Assault: Vulnerability in Windows, Mac and Linux
As appeared in the video shared by Rüzenberg, together with the initial three Thunderspy vulnerabilities, an assailant can break the security system set in place, manipulate the identity of a Thunderbolt gadget and get hold of an unapproved, malicious session with a Thunderbolt gadget.
In spite of the fact that this technique is new, this isn’t a security issue for Thunderbolt, and for some individuals, the assault doesn’t essentially expand the current hazard.
PCs and Operating Systems Vulnerable To Thunderspy Attacks
Thunderspy assaults deal with the Windows and Linux PCs of 2019 and before, which posses Thunderbolt Ports.
Also, the Thunderbolt Apple MacBooks (Retina adaptations sold since 2011) are powerless against the Thunderspy assault when the PC is running a Windows or Linux working framework.
Apple MacBooks can also be exploited through outsider or third-party apps such as web applications and remote code execution instruments.
Secure centre PCs make it a lot harder for aggressors, Sakib contends, “yet that does not mean they are invulnerable to Thunderspy. The DMA insurance of the bit is empowered of course, and this component keeps an aggressor from getting to the Thunderbolt port until the assault has gotten the casualty’s secret key”, he said.

Thunderspy Attacks Vulnerability of Windows, Apple and Linux
Conclusion on Thunderspy Attacks
Precautions Taken By Intel Against Thunderspy Attacks
To safeguard itself against this assault, Intel presented a component a year ago called Kernel DMA Protection that limits Thunderbolt gadgets to a specific measure of memory.
Precautions You Should Take Against Thunderspy Attacks
A resort suggested by the specialists was that users should exploit the Known security levels of Thunderbolt by restricting access to untrusted gadgets and also switching Thunderbolt off in the current operating system settings.